MD5 Generator
The MD5 Generator tool allows you to create MD5 hash values from any input text, providing a unique and fixed-size string that represents your data. This tool is perfect for developers, security professionals, and anyone who needs to generate MD5 hashes for data integrity verification, password storage, or file verification. The process is fast and reliable, ensuring accurate MD5 hash generation.
Share on Social Media:
Efficient MD5 Generator: Securely Hash Your Data
Instantly convert text to a secure and unique MD5 hash with our efficient md5 generator. A swift solution for maintaining data integrity, it delivers consistency and peace of mind with minimal effort.
Key Takeaways
The MD5 Hash Generator creates a unique 32-character hexadecimal hash for any given input string, providing a consistent digital fingerprint irrespective of the data size.
MD5 hashing is irreversible and deterministic, ensuring data integrity by producing the same output hash for the same input, although not recommended for all cryptographic purposes due to collision vulnerabilities.
Practical applications of MD5 hashes include securing passwords, verifying file integrity during transfers, with modern MD5 generator tools featuring batch processing and integration capabilities for enhanced efficiency.
Unlocking the Power of MD5 Hash Generator
Designed as a toolkit marvel, the MD5 Hash Generator creates unique hexadecimal hashes for input strings, thus preserving data integrity with each conversion. But what does that mean? Imagine having a tool that can take any piece of information, no matter how long or short, and convert it into a 32-character string. It’s like having a unique digital fingerprint for every piece of information you want to secure!
The MD5 hash generator impresses with its capabilities to encode any string or words, along with its consistent and versatile performance. Whether you’re hashing a single word or an entire novel, the MD5 hash generator ensures the output is always a 32-character string. This level of consistency is what makes MD5 such a reliable tool for data integrity and comparison.
Generating MD5 Hashes
The process to generate an MD5 hash is uncomplicated, starting with the user entering the plain text into a specified input box. This can be anything from a single word to an entire document. The next step is to click the ‘Generate’ button to initiate the MD5 hashing process. It’s as simple as that!
The moment the ‘Generate’ button is clicked, the magic happens. The plain text transforms into a unique MD5 hash and appears in an output box for the user to see and use. This hash, a 32-character string, is the unique identifier of the input string. No other input can produce the same MD5 hash, and that’s what makes it such a powerful tool for data integrity and comparison.
Understanding Output Format
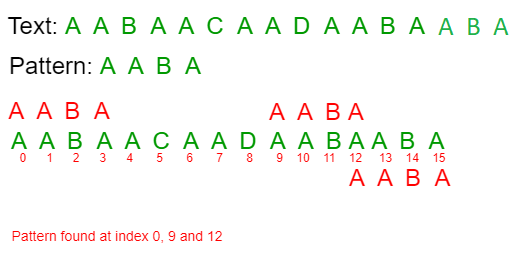
Despite the size of the input, the MD5 hash function consistently outputs a 128-bit hash value. This hash value is typically represented as a 32-character hex string composed of hexadecimal characters, which include the numbers 0-9 and the letters a-f.
You might wonder why the output is in this fixed-length, hexadecimal format. A standard output representation simplifies comparisons and guarantees data integrity, making it an integral part of the hashing process. Whether you’re hashing a word or an entire document, the output will always be the same length, making it easier to handle and compare.
The Essentials of MD5 Hashing
Message-Digest 5, or MD5 as it’s commonly known, is a prevalent hashing algorithm that computes a fixed-size bit string value from a data block. It’s like a complex mathematical mixer that takes in data, breaks it down, shuffles it, and spits it out as a unique fixed-size hash value.
The MD5 hashing algorithm shines through its process. It takes the data and:
Divides it into 512-bit blocks
Processes these blocks through a series of mathematical operations to update a 128-bit state
Results in a unique hash value, ensuring data integrity and security.
And the best part? The efficiency of the MD5 checksum generation depends more on input/output speed rather than computational overhead, emphasizing its practical utility in various applications.
The One-Way Street: Irreversibility of MD5
Irreversibility stands as a defining characteristic of MD5 hashing. It’s designed as a one-way function that is computationally infeasible to reverse. This means that once a string is hashed, you can’t reverse-engineer the original string from the hash. It’s a one-way street with no U-turns.
The irreversibility of MD5 hashing ensures that the original data cannot be retrieved from the hash value. This contributes to the integrity and privacy of the data, making MD5 an excellent tool for data encryption and protection. However, for cryptographic security and preventing collisions, more robust algorithms like SHA256 and SHA512 are often preferred over MD5.
Consistency in Hashing
The MD5 hash algorithm is known for its feature of consistency. It is designed to be deterministic, ensuring that the same input string will consistently produce the same output hash. This means that regardless of when or where you hash a specific string, the output hash will always be the same.
This consistent output provides a reliable way to verify data integrity. If the input remains the same, the output hash will also remain the same. Therefore, by comparing the output hashes, we can confidently confirm whether the data has remained unaltered.
This predictability guarantees the reliability of the MD5 generator as a tool for secure and stable hashing.
Practical Uses of MD5 Hashes
Beyond being a fascinating piece of cryptographic technology, MD5 hashes also find practical applications in our digital lives. From securing file transfers to validating API requests, MD5 hashes are at the forefront of data integrity and security.
Checking that files remain unchanged during transfer is a common usage of MD5 hashes. By comparing the MD5 checksum of a downloaded file with the original, you can ensure that the file has not been tampered with during the download process.
Another use of MD5 is in API communications, where an MD5 hash generated from concatenated variables combined with a secret API key serves to validate the requests.
Securing Passwords with MD5
Securing user passwords is a significant role played by MD5 hashes. When a user creates a password, rather than storing the actual password, the system saves the MD5 hash of the password. This means that even if someone gains access to the system’s database, they won’t be able to retrieve the actual passwords.
But how does the system verify the password when a user logs in? Simple. When the user enters their password, the system generates an MD5 hash of the entered password and compares it to the stored MD5 hash. If the hashes match, the passwords match, and the user can log in. However, due to known security vulnerabilities, MD5’s original implementation for data security has evolved towards authentication use cases.
Ensuring File Integrity
Files’ integrity during transfers is verified using MD5 hashes. This helps to confirm that the transferred files have not been corrupted or altered. When a file is sent from one system to another, an MD5 hash of the file is also sent. Upon receiving the file, the recipient system generates an MD5 hash of the received file and compares it to the received MD5 hash.
If the hashes match, it means the file was not altered during the transfer. Even a single bit change in the file results in a drastically different, irreversible MD5 hash, highlighting the algorithm’s high sensitivity to changes. This use of MD5 is effective against simple errors during file transfers but insufficient to defend against deliberate tampering by attackers.
Advanced Features of MD5 Generators
MD5 generators evolve along with the digital landscape. Modern MD5 generators are packed with advanced features that make them more efficient and versatile. This includes the ability to calculate MD5 checksums during the file copying process rather than before, to minimize read operations and save time.
Selecting an advanced MD5 generator tool is crucial for handling large files quickly and without consuming excessive system resources. Furthermore, modern MD5 generators often support a range of hash algorithms, which goes beyond simple MD5 hash generation to include verification of existing hashes, offering greater versatility.
Batch Processing Capabilities
One such advanced feature is batch processing. Certain MD5 generator tools provide batch processing, enabling users to generate MD5 hashes for multiple files in one go. Imagine being able to generate unique hashes for hundreds of files with just a few clicks!
This significantly enhances productivity by allowing simultaneous hash generation. It saves considerable amounts of time when generating hashes for multiple files, especially when compared to processing them individually. In a world where time is of the essence, batch processing is indeed a boon.
Integration with Applications
MD5 generators also boast integration capabilities, thus extending their versatility. Developers can integrate MD5 hash generators into their websites to secure data transfers and ensure message integrity.
Advanced MD5 generator tools often support various hash algorithms and can be integrated with other software to enhance the user experience. They are also useful in API integration, which includes validating incoming requests from a partner’s website and ensuring the authenticity of these requests.
Optimizing Your Use of MD5 Generators
Operating an MD5 generator goes beyond merely generating hashes; it also involves optimizing the process for optimal results. This involves choosing unique input strings for secure MD5 hashing and staying updated on hashing algorithms and security practices.
The risk of hash collisions in MD5 is significantly low due to the extensive number of possible hash outcomes, underscoring the need for unique input strings. Staying updated on the latest developments in hashing algorithms and security practices is crucial to ensure the highest level of security and performance when using MD5 generator tools.
Choosing Strong Input Strings
When using MD5 generators, it’s important to choose strong, unique input strings. While the risk of hash collisions in MD5 is significantly low due to the extensive number of possible hash outcomes, it’s always best to minimize this risk by ensuring your input strings are as unique as possible.
Remember, the more unique your input string, the more secure your MD5 hash. So, the next time you’re using an MD5 generator, make sure to choose a strong, unique input string for the best results.
Regular Updates and Maintenance
Similar to other software tools, it’s important to stay current with the latest trends in hashing algorithms and security practices while using MD5 generator tools. As technology evolves, so do the threats it faces.
Therefore, it’s essential to keep abreast of the latest security practices and updates to ensure the highest level of security and performance when using your MD5 generator. In fact, organizations are encouraged to transition from MD5 to more secure password hashing methods like bcrypt, Argon2, or scrypt to maintain the best security posture.
MD5 Generator free on PagesTools.com
PagesTools.com offers an efficient, free MD5 generator, an easy-to-use tool for those in search. It allows users to create MD5 hashes of strings by simply entering text and clicking the ‘Generate’ button.
PagesTools.com also offers a script that automatically generates checksums for newly uploaded resources to ensure their integrity. Users can even export metadata in CSV format, including data from all accessible fields, to view stored checksums.
The checksum functionality on PagesTools.com can be configured to block duplicate files based on their checksums, although this feature is disabled by default to avoid performance impact.
Summary
From understanding the power of MD5 Hash Generators to exploring their practical applications and advanced features, we’ve embarked on quite a cryptographic journey today. We’ve discovered how these tools, with their unique encoding of strings into fixed-length hexadecimal hashes, serve as a cornerstone of data integrity and security.
As we continue to navigate the digital universe, tools like MD5 Hash Generators will only grow in importance. So, next time you’re securing a password, verifying a file transfer, or integrating an API, remember the power of that 32-character string. Take a moment to appreciate the intricate mathematics and advanced technology that goes into creating that unique digital fingerprint. And remember, with the right tools and practices, the power to secure your data is in your hands.
Frequently Asked Questions
What is an MD5 Hash Generator?
An MD5 Hash Generator creates a unique hexadecimal hash for input strings, ensuring data integrity with every conversion.
How does the MD5 generator work?
The MD5 generator works by processing input strings through mathematical operations to produce a unique 128-bit hash value.
Can an MD5 hash be reversed?
No, MD5 hashes cannot be reversed, making it impossible to retrieve the original string from the hash.
What are the practical uses of MD5 hashes?
MD5 hashes have practical uses in checking file integrity, securing user passwords, and validating API requests. They are commonly utilized in various applications.
How can I optimize my use of MD5 generators?
To optimize your use of MD5 generators, choose strong and unique input strings for hashing and stay updated on the latest developments in hashing algorithms and security practices. This will help ensure better data security.